Spy bugs
Professional listening devices and spy bugs: what they are, how they work and how to remove them through environmental remediation.
The term environmental bug refers to every type of spy bugs, wires or spy cameras that can capture audios and/or videos, record them and transmit them remotely, in order to control people and environments in different situations.
In common knowledge, the use of bugs is often attributed to certain subjects, such as law enforcement officers, private investigators, intelligence and security operators. These tools can be nevertheless purchased by anyone. Yet, there are various types of environmental, economic or professional bugs on the market.
The cheap ones are easily available on internet and often with affordable prices for everyone. The professional bugs are instead miniaturized devices of high quality, used by professionals in environmental interceptions. They have different shapes and sizes and can be easily hidden even in very small objects, such as sockets, appliances, pens, USB sticks, lamps and wallets.
Types of spy bugs
How to Find Hidden Spy Cameras and Audio Bugs and how can we remove them?
Micro-bugs search and remediation involve seeking bugs, recorders, cameras, remote-controlled, switched-off or inactive equipment.
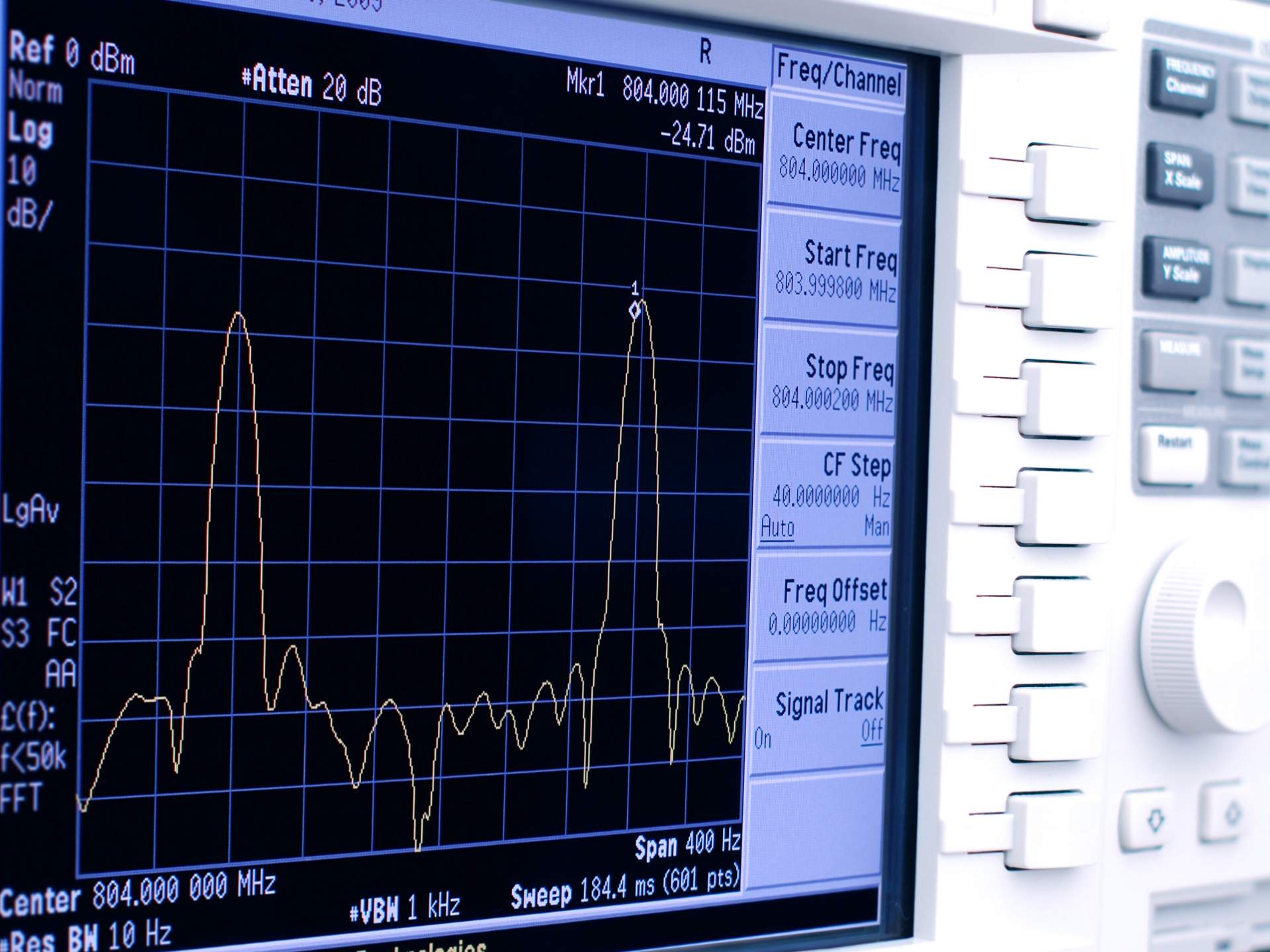
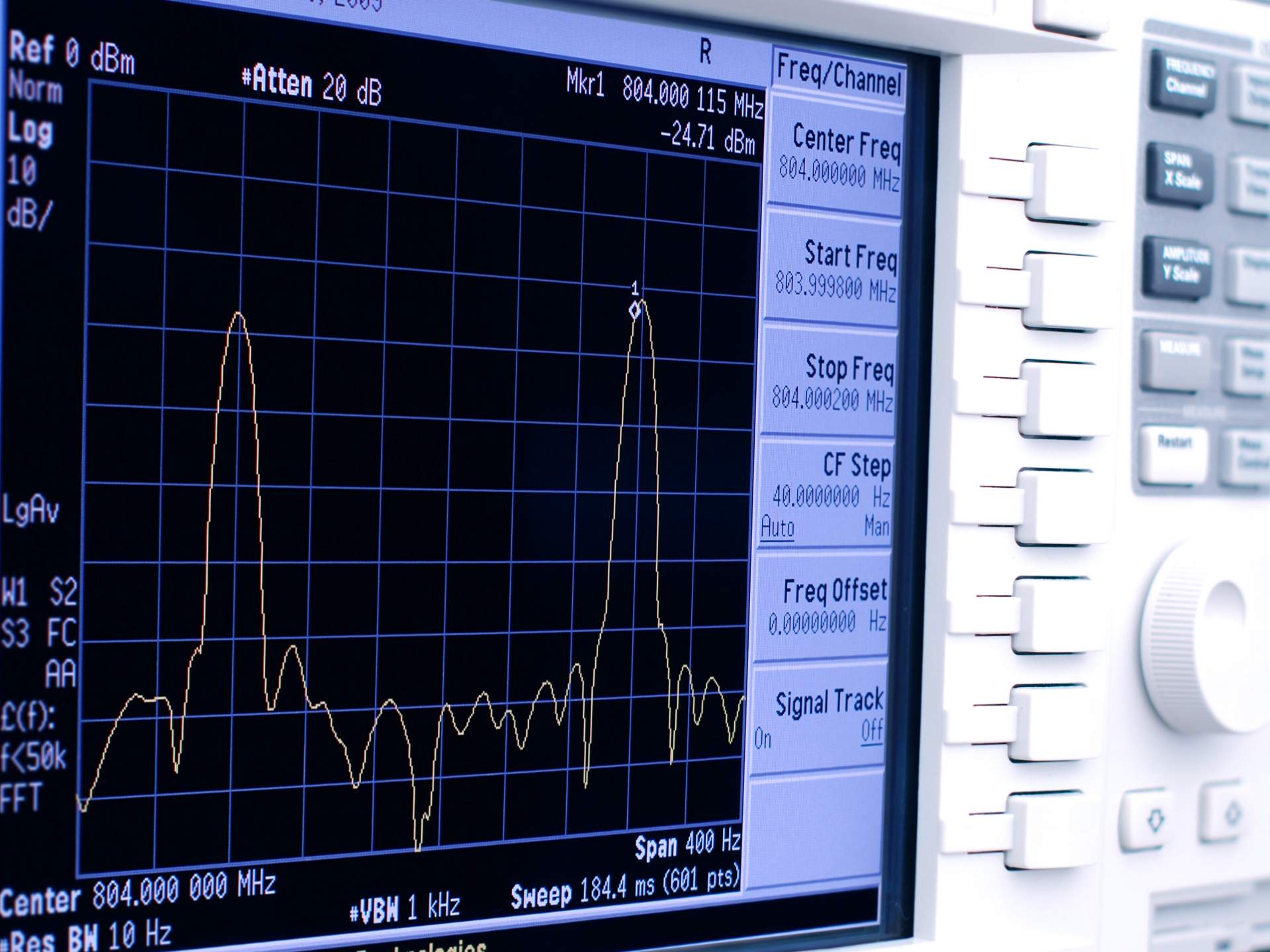
It is performed through physical inspections, instrumental checks of different nature and with electrical and electronic scans of each environment.
In relation to the different modern spy technologies, adequate countermeasures and appropriate equipment must be adopted. This is necessary in order to detect hidden, turned off or not working electronic devices, or unauthorized GPS devices which are often hidden in the car.
In this respect, Dogma owns the T.I.S.P. System® (TREATHS IDENTIFICATION and SECURITY PLAN), the innovative method that enables the interception of security threats and the identification of critical issues present in the places examined. Dogma is continuously engaged in professional training and in the acquisition of the most innovative technologies suitable to protect the integrity of its own customers.
In order to be able to offer this service, our technical team uses consolidated procedures and newest generation electronic instruments. The objective is to identify every bug present in meeting rooms, executive offices, cars or private environments, in order to guarantee the certainty of resuming communications in a secure manner.
Once bugs have been identified, timing and intervention methods are defined. At the end of each remediation, a technical report detailing all the results of the search for bugs is prepared. The Report also gives advice to avoid future criminal acts, such as the identification of at-risk environments and technologies, providing technical solutions to the problems therein highlighted.
When to request Environmental Bugs from Bugs.
Environmental remediations from bugs can be carried out both after the presence of bugs or wires has been detected, or in advance, when a suspicion exists of being under control or being intercepted.
The reasons that may lead individuals to perform such criminal offense in a business environment, range from unfair competition to general existing disputes among members, employees and collaborators. Economic issues, the desire to acquire customers or resources (technological or human) and corporate strategies also play a key role.
Our experience in this sector allows us to highlight some "indices of suspicion" such as:
- Unknown persons aware of the client's movements;
- Customer's confidential information reported by people who should not be aware of such information;
- Unusual sounds, noises or interferences detected on the telephone line or on the TV or audio system;
- Unexplained variations in the physical structure of the premises or signs of unauthorized entry;
Find out all the details and information to request environmental bug remediation.
Call and to immediately receive a quote and a confidential and free consultation, or use the form on the page to send us a request. You can also Activate online an investigation, find out how.
A site is not enough to solve all doubts and above all to meet all needs. Use the form on the side or the CHAT to contact us, book an appointment and ask us for information.